Are you aware of the different types of cybersecurity threats for small businesses? Do you have a plan in place to prevent them from occurring in the first place and to minimize the effects of a successful cyberattack?
Chances are, you already have antivirus and antispam software installed. However, this hardly covers all of the possible vulnerabilities that your business faces. We’re going to further discuss what types of cybersecurity threats you should be aware of for your small business and give you a few ideas on how to prevent them.
Malicious Software
Malicious software, typically known as malware, encompasses a wide range of software that is designed with the intent to steal data, wreak havoc on networks, take information hostage, or otherwise disrupt your daily business operations.
There are several types of malware that can affect your computers including spyware, ransomware, viruses, trojans, worms, and adware.
Spyware
Spyware is used to spy on a computer user’s actions; it is typically installed by someone who knows the owner of the computer or business. This type of malware often tries to steal passwords and banking information; it may also seek out your browsing habits and trade secrets.
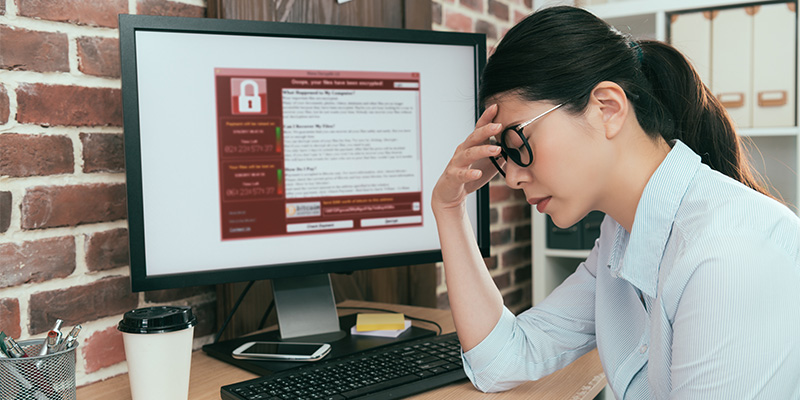
Ransomware
Ransomware is a type of malware that works to take control of data and encrypt it to make it unusable unless a ransom is paid. Often, ransomware is spread through malicious emails targeting specific users (phishing, spear-phishing).
Virus
A computer virus is a type of code that modifies a file. When the host file is opened, the malicious code is executed, infecting the rest of the computer. Similar to a human virus, it can spread to other computers and networks.
Trojans
Trojans act as harmless files or applications but can allow cybercriminals access to your infrastructure through installed backdoors or other types of malware. A trojan can’t self-replicate but can spread by other users on a network by opening infected files or attachments.
Worms
A worm is a type of self-replicating malware that spreads to other computers via messaging apps and email. Worms can modify or delete files; they can also install backdoors that cybercriminals can use later to access your system. Some worms have little purpose other than to deplete your computing resources.
Adware
Adware is thought to be one of the least harmful types of malware and is often installed with the download of a shady application. It’s usually responsible for skewed search results, slowed browsers, and pop-up ads. It can also pave the way for spyware to be installed.
After looking at each of these types of malware, you might believe that your antivirus software protects you or that your employees’ browsing habits wouldn’t cause any of these to be installed. This is untrue as cyber attackers are always finding ways around protective software and human error accounts for an incredibly high number of malware installations.
Phishing & Spear-Phishing
Phishing is the use of legitimate-looking emails and websites to lure a user into clicking on specific links or entering personal information or credentials. Typically, phishing attacks don’t target any specific individual but instead will cast a wide net to catch as many unsuspecting victims as possible.
On the other hand, spear-phishing specifically targets a high-value individual, account, or department. Spear-phishing attempts may include the names of executives, employees, and other specific information to add legitimacy to the attempt.
Weak Passwords and Poor Security Habits
Many websites require certain criteria when creating passwords – usually the use of at least one capital letter, a numeral, and a symbol. Sometimes, you can’t use actual words, previously used passwords, or repeating characters.
The reason behind this is that these websites know that cyberattackers will use dictionary attacks or brute force tactics to guess passwords. A dictionary attack will systematically use alphabetic dictionary entries to find a password while brute force attempts will submit multiple guesses.
Of course, once you’ve created a password that fits all of the requirements to prevent these attacks, you may choose to write it down. Doing this is a poor security habit and can help anyone who finds it guess your password; this is especially true if you use the same password for multiple accounts.
There are many types of poor security habits, all of which can negatively affect the overall cybersecurity of your small business. Other habits to be aware of include thinking that your business is too small to be a target, failing to update software, not installing software patches, avoiding the process of disaster recovery planning, not encrypting data, and not using multifactor authentication.
Malicious Insiders
Sometimes it’s easy to spot an employee who is unhappy within your organization or who has something to gain by sharing private information. Other times, you might be blindsided by this malicious insider.
Because it can be difficult to determine who is or isn’t a malicious insider, it’s important to have cyber security in place to protect against this type of threat. The best way to do this is by having monitored user access and by practicing the principle of least privilege.
Monitored user access and the principle of least privilege go hand-in-hand. By monitoring each user’s access, you can determine exactly what data can be seen, modified, shared, or deleted. The principle of least privilege basically gives each user the exact amount of access needed to do their job. The combination of these two cybersecurity measures helps to prevent a malicious insider from gaining too much access while still allowing each employee the ability to perform needed tasks.
Effects of Poor Cybersecurity
Having poor cybersecurity practices can open your small business up to a range of attacks from each of the threats listed here. No matter how small your business is, the amount of sales volume, or the types of data you deal with, poor cyber security can make you a target of cybercriminals.
Companies who become victims of cyber attacks will often lose the trust of their clients, which can lead to a loss of business or months of dealing with angry customers. Additionally, you may face legal fines or fees from your industry’s governing organization for not following standard security procedures.
If this isn’t enough, your IT infrastructure and networks could face irreparable damage, costing you thousands of dollars to rebuild or replace components.
How to Protect Your Business from Cybersecurity Threats
Cybersecurity is an ever-changing landscape. There are numerous threats that already exist and hundreds more are discovered each day. Having antivirus software installed is a nice start but is far from the level of protection your business needs to prevent attacks and protect sensitive data.
Helping your employees learn cybersecurity best practices can help mitigate some risks, but the ultimate way to stop these security threats in their tracks is to hire a company that offers a range of cybersecurity protection for small businesses.
If you would like to learn more about any of the cybersecurity threats for small businesses mentioned here or would like to implement the use of a professional cyber security company to protect your digital assets, contact High Point Networks today for a consultation.